Tonight I finally got around to installing the recently released Windows Server Technical Preview 2, which was published around the time of the annual BuildConf in the US.
So I ran up a Hyper-V image and hit the standard product selection screen. I was greeted, as it has been rumoured, with two options – Server (no tools, i.e. core) or Server (with Admin tools). This is suspiciously different to Windows Server 2012 R2 in that there’s no Server plus Graphical User Interface option.
I elect for the Admin tools, and continue.
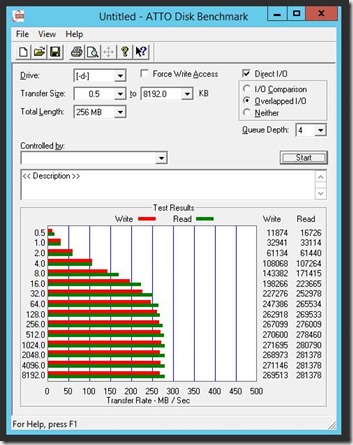
The usual copying of files, it doesn’t take too long to get up and running. I suspect the OS is fairly lean in terms of disk consumption, given how fast the install took. First thing in and it’s off to set the Administrator password.
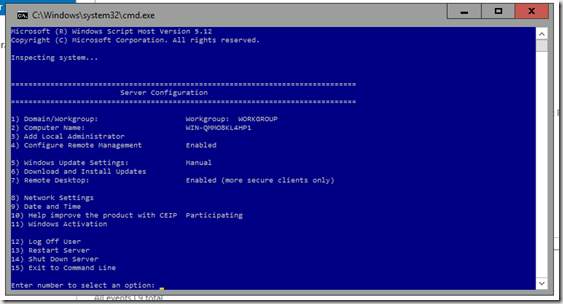
Authenticated, and up comes the familiar Server Manager. It used to annoy me that Server Manager would launch by default, but given the reality of no GUI, it’s my last bastion short of PowerShell scripting everything.
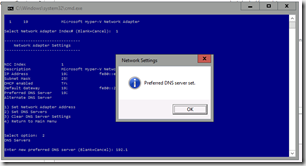
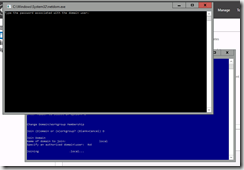
So the first thing I do is change the Computer name, this is easily done via the old faithful System applet – however I need to also configure the Ethernet since my Lab setup (when using DHCP) doesn’t include my domain DNS as primary (i.e. I can’t join the domain right away). Configuring networking got console-like:
So I also decided to change add the VM to the domain as well using the console tools. It was actually very simple. I’m going to wonder why I ever needed a GUI..
After a quick(ish) reboot, we’re back – except now I’ll authenticate using my Domain credentials instead.
Before I do anything further, I take a checkpoint in case I bork anything up; and then resume to do some role-based installs.
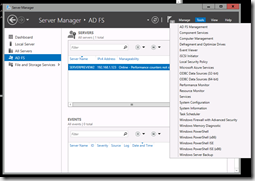
Installing Roles – ADFS vNext
Since I’ve been working with Active Directory Federation Services (ADFS) lately, I’m curious if this preview contains any advances, so..
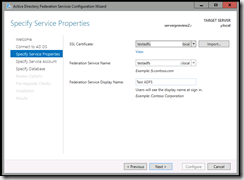
So I jump into an MMC console and add the Certificates snap-in, selecting Local Computer. From here I request a new certificate from my local CA:
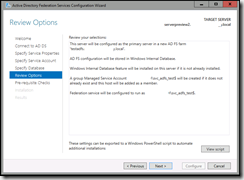
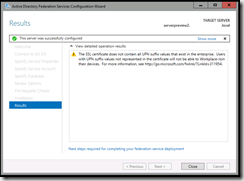
The options haven’t changed much, I elect to have a new service account created for me and off we go.. Behold, we have success:
Examining the next version of ADFS – Version 4?
The “current” version (shipping with Server 2012 R2), according to binary/product version is 6.3:
Microsoft.IdentityServer.Service, Version=6.3.0.0,
The version shipped with Windows Server Preview 2 is version 10:
Microsoft.IdentityServer.Service, Version=10.0.0.0
Officially, the version which ships with Windows Server 2012 R2 is AD FS 3.0, so I’m not sure if this next version should be v4.0 or not.
The first interesting thing – no Internet Information Services requirement. The second… check out the differences between the current ADFS and the one in the Technical Preview 2:

AD FS 3.0 (Windows Server 2012 R2) vs.

AD FS ?.0 (Windows Server vNext)
Clearly there are some big changes ahead. Hopefully, it’ll be the introduction of OpenID Connect and full OAuth2 authorization flow support…. So I clicked on the “What’s new in AD FS?” link, but alas, fail:
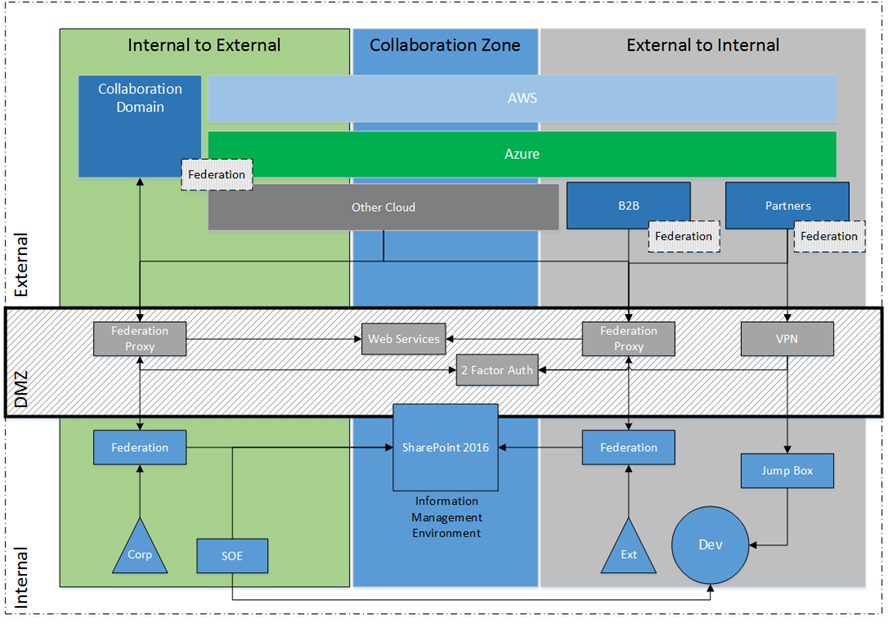
Moving along we come to – scopes – and look at the juicy options, which includes OpenID Connect:
Plus, AD FS now can issue certificates for User Logon and VPN access:
Finally, some new endpoints to play with. Notice OAuth2 is enabled by default:
We now also have a separate window for managing clients, which gives us most of what we need for proper OAuth2 – see my previous article about Identity Server.
The wrap-up
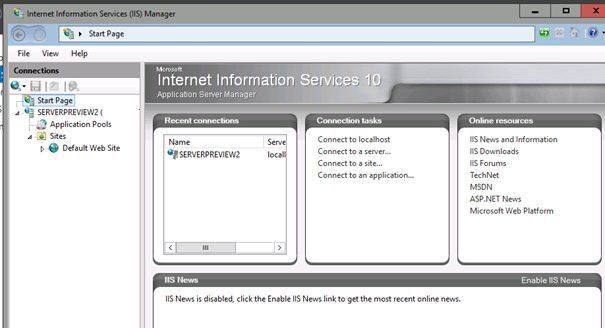
Well, that’s enough for one article. I’ll start playing with ADFS (v4.0?) and see whether it can do everything I think it can do. In the meantime, I’m going to install the next version of Internet Information Services 10 (IIS) and see what’s changed there, too.
Until next time.