Today I found myself in an odd situation where I wanted to access the SQL Server instance of a Windows Update Services (WSUS) instance, so I could perform some basic maintenance to reduce the DB’s disk and memory footprint. This instance of WSUS has been running for a few years without a lot of TLC (the occasional clean up) and is performing like a dog.
Since I’m a dummy, I didn’t check that my administration account was a member of the “WSUS Administrators” security group, and as such I could not use SQL Management Studio to access the WSUS 6.0 SQL Database at: \\.\pipe\MICROSOFT##WID\tsql\query
So instead, I decided to try and access the database as the NT AUTHORITY\SYSTEM account, which I knew for certain did have access. I found a very helpful blog entry which uses PSExec to accomplish the feat. The rest is from that article (linked below). I’m throwing in (at no extra cost) the updated path for the latest version (as of January 2018) of SSMS (v17.4).
“PSExec tool gives you an option to run a remote process or an application using System account, if SYSTEM account has permission on that application.
For example, if SQL Server has NT AUTHORITY\SYSTEM as one of its logins, then you can use this account to login to SQL Server. However, you can’t use SQL Server Management Studio or sqlcmd to login to SQL Server using NT AUTHORITY\SYSTEM.
However, PSExec gives you an opportunity to login to SQL Server using NT AUTHORITY\SYSTEM. Once you download PSExec tool bundle from http://technet.microsoft.com/en-us/sysinternals/bb897553.aspx”
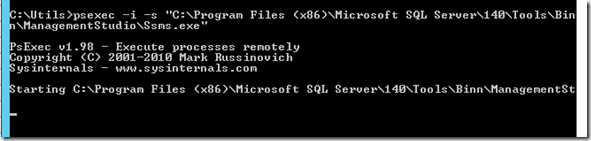
C:\Utils>psexec -i -s “C:\Program Files (x86)\Microsoft SQL Server\140\Tools\Binn\ManagementStudio\Ssms.exe“
PsExec v1.98 – Execute processes remotely
Copyright (C) 2001-2010 Mark Russinovich
Sysinternals – www.sysinternals.com
Bonus
Here’s what you might consider doing once you get access to the WSUS DB:
https://www.3ait.co.uk/blog/solved-shrink-a-wsus-database-susdb-mdb-to-almost-nothing-2


One thought on “Access SQL Server as NT AUTHORITY\SYSTEM using SSMS and the PSExec tool”
Hi there. I’m trying to gain access to the SQL server with PsExec.exe, but when I run the command, it says that the SSMS is already running, yet I have made sure that it is not running. Please advise as I have checked that there is only the Instance in which I wish to log into running and I have restarted my Laptop.
Any help would be highly appreciated.
Thanks